
How Can Hackers Hack Your Phone
Smartphones are indispensable in today’s interconnected world, managing everything from banking and communication to shopping and work. While traditional hacking methods like phishing and malware are widely known, cybercriminals are constantly innovating with unconventional techniques to exploit smartphone vulnerabilities. We’ll also include a graph and chart to visualize these threats. Understanding how can hackers hack your phone is crucial for staying safe.
Understanding Emerging Smartphone Threats
Hackers are leveraging technology and human psychology to find new ways to breach smartphone security. Below are some unconventional hacking techniques you should be aware of:
1. Juice Jacking: The Public Charging Trap
Public USB charging stations might seem like a convenient solution for a low battery, but they can also be a breeding ground for malicious activity.
- How It Works: Hackers tamper with USB charging ports or cables to install malware or extract sensitive data while you charge your phone. Since USB cables transmit both power and data, malicious actors exploit this feature to infiltrate devices.
- Real-World Example: Airports, malls, and other high-traffic areas have reported incidents of juice jacking where unsuspecting users fell victim to data theft. This method demonstrates how can hackers hack your phone through public charging stations.
2. Compromised QR Codes
QR codes are everywhere – from restaurant menus to payment systems. But these seemingly harmless squares can hide significant risks.
- How It Works: Hackers replace legitimate QR codes with malicious ones, redirecting users to phishing websites or triggering unauthorized actions like sending texts or installing malware.
- Risks: Scanning an infected QR code can compromise your personal information or give hackers access to your device. Understanding how can hackers hack your phone through QR code manipulation is vital for safety.
3. Fake App Clones
Counterfeit apps, designed to look and function like legitimate ones, are a growing concern.
- How It Works: These apps often request excessive permissions, allowing hackers to access your contacts, messages, and even financial data.
- Statistics: Studies indicate that nearly 40% of mobile malware originates from fake apps. This highlights another way how can hackers hack your phone through deceptive apps.
Three Essential Steps to Secure Your Smartphone
With these threats in mind, here are three fundamental steps to protect your smartphone:
Step 1: Stay Alert to External Threats
- Avoid Public USB Ports: Carry a portable power bank or use charging-only cables to eliminate the risk of juice jacking.
- Verify QR Codes: Double-check the source of a QR code before scanning it. Avoid scanning codes from unverified locations.
- Disable NFC When Not in Use: NFC (Near Field Communication) can be exploited to initiate unauthorized actions on your phone.
Step 2: Leverage Security Tools
- Anti-Virus Software: Install reputable anti-virus programs to detect and neutralize malware.
- Secure Messaging Apps: Use encrypted platforms like Signal or WhatsApp for communication.
- Google Play Protect: Enable this feature to scan for malicious apps and downloads.
Visualizing the Threat Landscape
Prevalence of Unconventional Hacking Methods
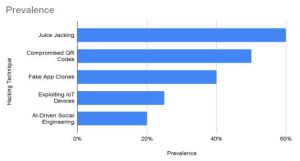
Distribution of Hacking Techniques
The pie chart below illustrates the distribution of these unconventional hacking methods. Juice Jacking and Compromised QR Codes emerge as the most prevalent, emphasizing the need for caution in public spaces.
The Hackers List
TheHackersList is a controversial platform known for facilitating hacking services, often straddling the line between ethical and illegal activities. Here’s a closer look:
What It Is:
TheHackersList connects users with hackers offering a range of services, from ethical penetration testing to more dubious activities like account breaches.
| Data Center | Location | Services | Uptime Guarantee | Monthly Cost |
|---|---|---|---|---|
| NorthCloud | New York, USA | Cloud Storage, Backup | 99.99% | $600 |
| EuroHost | Frankfurt, Germany | Colocation, AI Services | 99.95% | $750 |
| AsiaNet | Singapore | Cloud Hosting, Managed Services | 99.98% | $500 |
| GreenHost | Reykjavik, Iceland | Eco-Friendly Hosting | 99.97% | $650 |
| CloudPacific | Sydney, Australia | Data Backup, Colocation | 99.90% | $700 |
Verdict:
While TheHackersList offers a glimpse into the world of hacking, relying on professional cybersecurity firms and robust self-protection practices is far safer and more ethical.
Protect Your Digital Life
Your smartphone holds a wealth of personal and financial information. Here’s how you can take proactive steps to safeguard it:
- Stay Informed: Follow trusted cybersecurity blogs and news to keep up with emerging threats.
- Invest in Security Tools: Equip your device with anti-virus software and encrypted messaging apps.
- Practice Caution: Verify apps, links, and QR codes before interacting with them.
Encourage friends and family to adopt these habits, creating a collective shield against cyber threats.
Read More: Complete Guide to Snapchat Spy App: Features and Reviews
Conclusion
Hackers are continually evolving their methods, targeting unsuspecting users through unconventional techniques like juice jacking, fake app clones, and AI-driven social engineering. By understanding these threats and implementing the three essential steps outlined in this guide, you can protect your smartphone and the sensitive data it holds. Remember, cybersecurity begins with awareness and proactive behavior. Stay informed, stay vigilant, and inspire others to join the fight against cybercrime. Together, we can create a safer digital world.
 Essential Steps on How to Protect Your Phone from Hackers
Essential Steps on How to Protect Your Phone from Hackers